What is the Enterprise Perspective?
Contents
1 Introduction
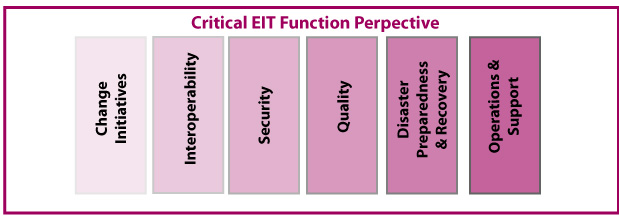
When thinking about what Enterprise information technology (EIT) does on a day-to-day basis, you have to consider two perspectives. First, there is a set of critical EIT functions that need to be attended to in order to guarantee the ongoing health and proper functioning of the EIT department as a reliable supplier of information and communication services to the enterprise. Functions—such as ensuring interoperability between systems and information systems security—never go away. These functions need to be executed well if the EIT mission is to be fulfilled. They are constant considerations to which EIT needs to pay attention.
In addition, to build its portfolio of information services, EIT develops solutions or systems for the enterprise, and those systems go through a lifecycle—a set of phases—from the initial idea, to collecting requirements and building a design, all the way to the retirement of the solution. These phases or sets of activities are well understood, and numerous techniques and processes have been developed to help EIT professionals execute this lifecycle.
In the EITBOK, we cover both project and product lifecycle phases as well as ongoing critical functions of the EIT organization. Part 1 addresses the critical EIT functions. Part 2 discusses the service lifecycle, from service concept—defined in a set of requirements—to service transition, to deployment, and then to retirement.
2 Overview of the Enterprise Perspective Chapters
2.1 Enterprise Architecture
Enterprise architecture (EA) is the practice of conducting enterprise analysis, design, planning, and implementation using a holistic approach for the successful development and execution of strategy. EA applies architecture principles and practices to guide organizations through the business, information, process, and technology changes necessary to execute their organization's strategies.
2.2 Enterprise IT Strategy and Governance
Prior to 2000, EIT was often viewed as an order taker from other departments of the enterprise; however, the amount of infrastructure and applications required to successively manage an enterprise in the 21st century, whether large or small, means that EIT is now intimately involved in the enterprise's day-to-day operations. Today, EIT needs to be viewed as a strategic partner to all the other functions and business units within an enterprise. This means that the results produced by EIT along with its effectiveness and efficiency are all critically important to the success of the enterprise. Careful strategic planning is required.
To ensure that the desired strategy is being executed, governance measures need to be established that monitor EIT responsibilities and accountabilities as well as supplier contracts, service-level agreements, and so on. Governance can be aligned with business functions or business processes (e.g., supply chain, quote-to-cash, finance, human resources, order-to-delivery, and quote-to-order), or it can be aligned by function or phase. Regardless of how the governance framework is implemented, governance needs to be connected to the entire process of supervising and maintaining all EIT resources.
2.3 Quality
Quality is a critical concept that spans the software and systems development lifecycle. Quality is defined by establishing a set of attributes that are critical to a product or service being delivered. These attributes enable the selection of measurements that can and should be used to assess the service or product quality. Whether we are conscious of it or not, the definition of quality is essential to the successful creation, production, and consumption of all products and services. It does not simply live within the Quality department, nor is it simply a testing stage following development. Rather, it is a pre-defined set of attributes that must be achieved to ensure that the product, service, or system being delivered creates the greatest sustainable value when taking account of the various different needs of all the stakeholders involved.
2.4 Security
EIT security's goal is to preserve the confidentiality, integrity, and availability of information and information systems. The principles behind an organization's information security management system (ISMS) need to design, implement, and maintain a coherent set of policies, processes, and systems that keep the risks associated with the breach of its information assets at a tolerable level. And yet, the team must also manage the cost and inconvenience of managing the risk.
2.5 Interoperability
In the enterprise, information needs to be exchanged in order to get a job done, or to achieve a defined objective of the enterprise. When information cannot be shared automatically by one system or person with another, that information is manually copied, manually updated in one or more private local versions, or otherwise re-created by the other person or system. Employees who know the data exists find a way to get it, usually through undocumented manual processes.
Interoperability refers to the ability of systems (including organizations) to exchange and use exchanged information without knowledge of the characteristics or inner workings of the collaborating systems (or organizations).
2.6 Operations and Support
The operations and support phase involves performing the activities and processes required to deliver and manage services provided by EIT assets to business users and customers, at agreed-to levels. This phase is all about maintaining an operation normal state in the EIT environments, meaning that systems and processes execute according to expectations, with no surprises.